The landscape of digital asset recovery has shifted dramatically in 2026. Decentralized finance (DeFi) protocols are growing more complex. Furthermore, privacy-enhancing technologies like zero knowledge proofs have evolved. Consequently, the old “copy-paste” investigative methods are no longer effective. At Ethical Asset Solutions, the investigative framework relies on a combination of proprietary blockchain forensics and real-time data.
Understanding the technical “how” behind an investigation is the first step for any observer. Specifically, professional blockchain forensics is not a “hack.” Instead, it is a meticulous forensic audit. This process maps the movement of value across a complex ledger. Below, we explore the specialized toolkit used to track and identify the flow of illicit funds.
1. Heuristic Clustering and Address Labeling
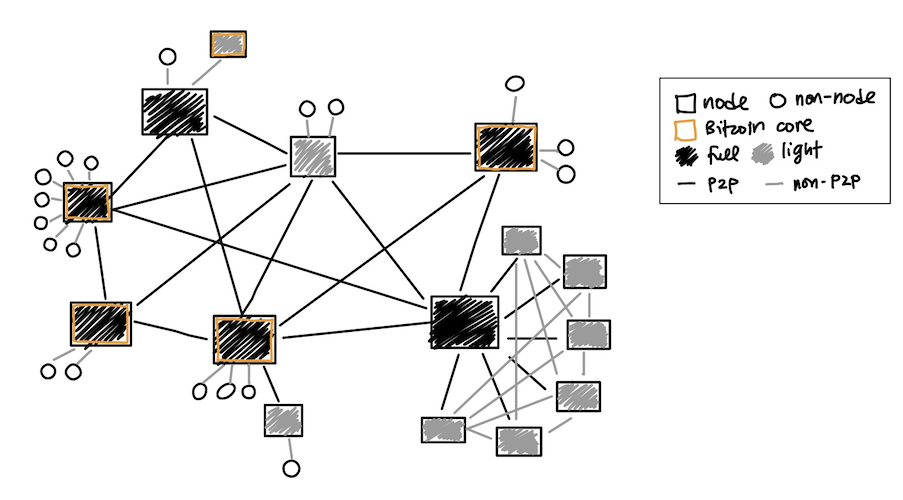
On-chain data is pseudonymous by nature. However, it is rarely truly anonymous in the hands of a specialist. Through Heuristic Clustering, investigators analyze patterns in transaction behavior. This allows for the grouping of multiple “anonymous” wallet addresses into a single controlled entity.
For instance, entities often move funds from several distinct wallets into one “consolidation” address. If they interact with the same smart contract in a predictable sequence, forensic tools identify them as one organization. Therefore, it is possible to map the entire financial infrastructure of a network. This high-level mapping was a core component of the MNCTN Global forensic audit.
2. VASP Attribution and the FATF Travel Rule
The ultimate goal of most illicit actors is to convert digital assets into cash. To achieve this, assets must eventually move to a Virtual Asset Service Provider (VASP). Usually, this is a centralized exchange.
The modern toolkit monitors these “off-ramps” in real-time. In 2026, investigative methodology strictly aligns with FATF Recommendation 16 (The Travel Rule). This rule mandates that VASPs share sender and recipient information. By utilizing a database of millions of exchange-hosted addresses, investigators can identify exactly where assets are liquidated. This data is essential for the technical documentation required by authorities. This process is further explained in our technical security reviews of Kraken and Gemini.
3. Cross-Chain Forensics and Bridge Tracking
In 2026, sophisticated actors frequently use “Chain Hopping” to hide their tracks. They move stolen Ethereum to the Bitcoin network or swap assets for various altcoins. Consequently, forensic suites now include cross-chain tracking capabilities. This allows the investigator to follow the “value” even when it changes form.
By monitoring bridge liquidity pools and decentralized exchange (DEX) swaps, a continuous “chain of custody” is maintained. This is vital when dealing with evolved “Pig Butchering” scams. These incidents often involve moving funds across multiple blockchains to confuse traditional auditing methods.
4. Digital Forensics and Off-Chain Intelligence
A blockchain audit is only half the battle. To unmask the individuals behind the screens, investigators employ off-chain digital forensics:
-
Infrastructure Tracing: Identifying the hosting providers and IP addresses used by illicit platforms.
-
Metadata Analysis: Examining the code of decentralized applications for hidden footprints.
-
Social Markers: Analyzing communication logs to identify time zone specific activity or linguistic patterns.
5. Forensic Report Preparation Standards
The most advanced toolkit is useless if findings cannot be translated for official review. Therefore, a core part of the process is the generation of a Certified Forensic Audit Report. These reports translate complex blockchain data into a format that legal authorities can utilize. The focus remains on “Admissible Evidence,” ensuring every transaction is documented with a clear cryptographic “paper trail.”
6. Real-Time Liquidity Monitoring
Tracking a transaction hash is only the beginning. Modern forensics includes automated alerts for “dormant” wallets. When funds that have been stationary for months begin to move, it triggers an immediate notification. This allows for rapid coordination with exchange compliance teams. Speed is essential in 2026, as automated “mixers” can obscure funds quickly once they start moving.
7. Smart Contract Vulnerability Analysis
Many modern thefts occur through “malicious approvals” in DeFi. Investigators use tools to analyze the smart contracts that users interacted with. By identifying the specific function used to drain a wallet, it is often possible to trace the developer’s original wallet or “owner” address. This “backdoor” tracing is a specialized part of the toolkit that bridges the gap between software engineering and financial forensics.
The Importance of Technical Transparency
The digital asset industry is often plagued by groups promising “guaranteed” returns using “secret software.” In contrast, professional forensics relies on transparency. The blockchain is not “hacked”; it is audited using international financial standards. This process is built on data integrity, which is the only evidence that holds up during a VASP compliance dispute or a formal audit.
Leave a Reply